Access Control Systems versus Mechanical Keys and Locks
Physical access control systems offer several compelling advantages over traditional mechanical key and lock systems, making them a preferred choice for organizations and businesses of all sizes.
They provide enhanced security through customizable access rights, allowing administrators to control who can access specific areas and at what times. Unlike mechanical keys that can be easily duplicated or lost, leading to potential security breaches, electronic access systems can be instantly updated or deactivated, ensuring only authorized personnel have entry.
These systems offer superior tracking and auditing capabilities, logging each entry and exit with precise timestamps, which is invaluable in monitoring and investigating security incidents. Additionally, the flexibility of these systems allows for easy integration with other security measures like alarms and surveillance cameras, creating a comprehensive security solution. In contrast to the limitations of mechanical locks, physical access control systems represent a scalable, efficient, and more secure approach to safeguarding premises.
Credentials
Physical Access Control System (PACS) credentials are a critical component of modern security systems, used to manage and restrict access to physical locations like buildings, rooms, or sensitive areas. These credentials come in various forms, such as keycards, fobs, or biometric data, and serve as a means to authenticate an individual's right to enter a specific area.
Credential Readers
Once you have made the decision to deploy a Physical Access Control System (PACS) at your facility, it will soon be time to make decisions about the technology and aesthetics of the system. For instance, you will need to decide what types of credential readers to install. This decision will be impacted by the functionality, user experience, and threat posture at your facility all of which are often determined by a thorough risk assessment commonly performed by a security consultant.
Reader & Credential Format Options: Wiegand and OSDP
In the security industry, two primary options are available when it comes to access control system protocols for readers and credentials: OSDP and Wiegand. For those requiring the most secure protocol, be sure to choose OSDP.
Electronic Locks
Locking a door is a basic strategy to keeping unwanted visitors out of an area. However, how do you maintain a locked door and reduce friction by allowing authorized people in without issuing mechanical keys?
Electronic locks for doors secured and controlled by Physical Access Control Systems (PACS) are a critical component of modern security systems, used to manage and restrict access to physical locations like buildings, rooms, or sensitive areas. These locks come in various forms and functions, such as electromagnetic, electric strike, electric bolt, and more, and serve as a means to physically control the door to a specific secure area.
System Architecture
When it comes to vetting and designing your new Physical Access Control System (PACS), there are a few key features to consider. First, be sure to be working with a trusted security consultant. Next, consider the top system architecture considerations that Ari and Alex outline in this video.
Request to Exit Detectors
Building codes are written to help balance security, safety, and standard operations . That is, the ability of building owners to keep unauthorized people out while enabling people within the building to exit quickly and easily in case of a fire.
Many door designs use mechanical means to open a door in case of emergency. However, this can be difficult to accomplish with an electromagnetic lock (maglock) as part of the design. That’s why life safety codes and Authorities Having Jurisdiction (AHJs) will require at least one, and sometimes two, methods to guarantee that building occupants can evacuate quickly in case of emergency. This concept, making it easy to leave a building in case of emergency, is called free egress.
Securing request to exit (REX) detectors through sequential logic
Securing REX detectors is critically important when it comes to designing access control systems to ensure the integrity of a high security space. Sequential logic can be implemented to enhance the security of these detectors.
By employing sequential logic, a system can be engineered where a series of specific events or conditions must occur in a pre-defined order before a request to exit is granted. For instance, before the REX detector activates the door release, it might first require a valid card swipe followed by a motion detection event within a specified time frame. This approach not only ensures that the exit request is legitimate but also significantly reduces the chances of false activations or unauthorized access. Proper implementation of sequential logic helps in thwarting tailgating and piggybacking attempts, ensuring a tighter and more effective security regime for controlled areas.
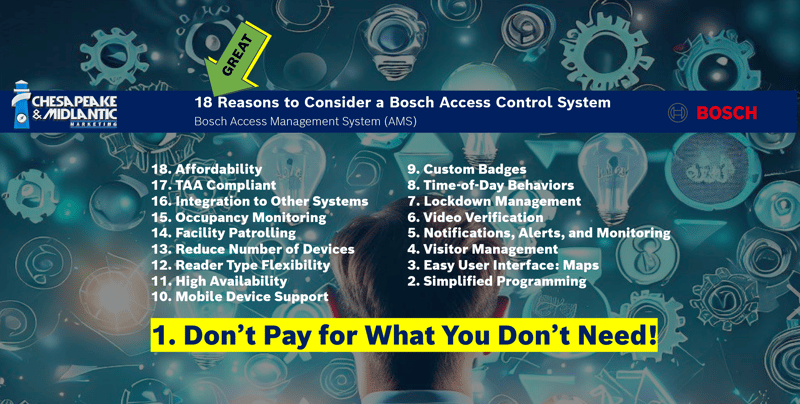
18 Great Reasons to Consider the Bosch Access Management System (AMS)
Bosch is known globally for manufacturing well-engineered, feature-rich security systems, and their access control solution is no exception. In this video, Ari lays out his top 18 GREAT reasons to consider a closer look at the Bosch access control solution, Access Management System (AMS).
Bosch Access Management System (AMS) is an access control system for stand-alone application or for integration with other systems, such as the Bosch video management system BVMS or Bosch B and G series intrusion panels.
- As a stand-alone system, it features a simple-to-use map and alarm viewer for a rapid assessment of all the devices and entrances on the site.
- As an integrated system, it allows the operator of a video management system to perform door-related tasks like video-based ID verification, to grant and deny access, or to disable doors.
- Intrusion areas can be armed directly from the Map View, and intrusion panel users can be centrally managed.
- AMS combines the robustness, performance and features of high-end access control products with a modern UI that makes it faster to install and configure.
- The existing portfolio of Bosch access control devices can be easily scanned and integrated.
- Data privacy and IT security is state-of-the-art, in order to comply with the latest data-protection regulations.
Download Ari's 18 Great Reasons Tip Sheet here >>
Bosch AMS System Overview
Access Management Server
The server is the main component for processing all data. It coordinates the activities of all the hardware and software components described below.
Master Access Controller (MAC)
The MAC is an additional security layer to increase system availability. It holds its own database to exchange information between AMCs, even if the main server or the network is down. All AMCs connect via highly encrypted communication to the MAC servers.
Access Modular Controller (AMC)
The AMC is a robust and reliable field controller to connect to up to 8 doors with readers and door strikes. With its large on-board memory the AMC can make autonomous decisions and store hundreds of thousands of access events, regardless of network interruptions.
Access Management Database
The SQL server holds all master data (cardholder, cards, authorizations, schedules, etc.) and all access events. The latest version provides encryption to protect personal information from misuse or theft, and can run on a dedicated server.
Access Management Dialog Manager
The Dialog Manager is the main user interface for configuring the system, and for collecting and maintaining access-related information. In particular, its personnel dialogs are used for enrolling new cardholders, and maintaining their access authorizations and credentials.
Access Management Map View
The Map View is a simple-to-use application both to visualize the overall security situation of the premises, and zoom into close detail. It displays access violations, tampering and malfunction alarms, and allows the sending of commands directly from the maps themselves.
Badge Designer
Card personalization is included in the product, providing you with the means to design your badges, to perform image acquisition with USB cameras and to use most commercially available card printers.
Visitor Management
Visitor Management is included in the AMS PRO license bundle.
- Receptionist view: a browser-based user interface where receptionists can efficiently register and monitor visitors and visits.
- Host view: a browser-based user interface where employees can pre-register their visits and receive email notifications when their visitor has arrived.
- Visitor view: a browser-based user interface in kiosk mode, where visitors can maintain their own stored profiles, scan their ID papers and digitally sign required documents, so substantially reducing waiting times and crowding at reception.
Access Management BVMS Interface
The seamless integration with Bosch Video Management System (BVMS) (version 10.1 or higher) allows the video verification of cardholder identities from the BVMS operator client: a person requesting access with a valid card can be manually verified through camera live stream and the cardholder’s photo from the database. Camera events can trigger door actions. Door events can trigger camera actions.
Access Management Intrusion Interface
Management of up to 50 B and G Series intrusion panels, and up to 500 panels for user management. Shows area states (e.g. armed, ready to arm), detector states and intrusion events on Map View. Allows the sending of commands (e.g. arm, disarm) to panels.
Access Management API
This REST-API facilitates the integration of 3rd party systems with AMS, for instance an Identity Management or Facility Management app.
Integration of wireless online locks
Integration of SimonsVoss SmartIntego wireless online locks (lock cylinders, door handles and padlocks) for doors, which require medium-level security, such as offices and classrooms. Available in certain countries only.
Integration of remote offline locks
Integration of OSS-SO compliant offline locks or Normbau (Pegasys) offline locks for remote doors, which connection via cabling is not possible due to distance, construction conditions or cost. Available in certain countries only.
Access Importer/Exporter
This tool facilitates data import and export from external systems for 1-time data migration, such as from Access PE systems, or regular data transfer from Active Directory via the LDAP protocol. An export of time stamps to an external Time and Attendance system is also possible.


%20Tip%20Sheet.png?width=200&height=158&name=18%20Great%20Reasons%20to%20Consider%20the%20Bosch%20Access%20Management%20System%20(AMS)%20Tip%20Sheet.png)